Share Post:
In educational environments like schools, access to certain websites and online services is often restricted through firewalls. These limitations, while intended to maintain a focus on education and ensure a safe browsing environment, can sometimes block access to legitimate educational material.
Using VPN and Proxy Servers are among the best ways to bypass a school firewall, but there are other effective methods we will talk about today.
Table of Contents
Toggle1. VPN

Virtual Private Networks (VPNs) are a popular and effective method for bypassing school firewalls. They not only provide access to restricted websites but also ensure your online activities remain private and secure. This can be a great solution for School Chromebooks as well as other devices.
How VPNs Work?
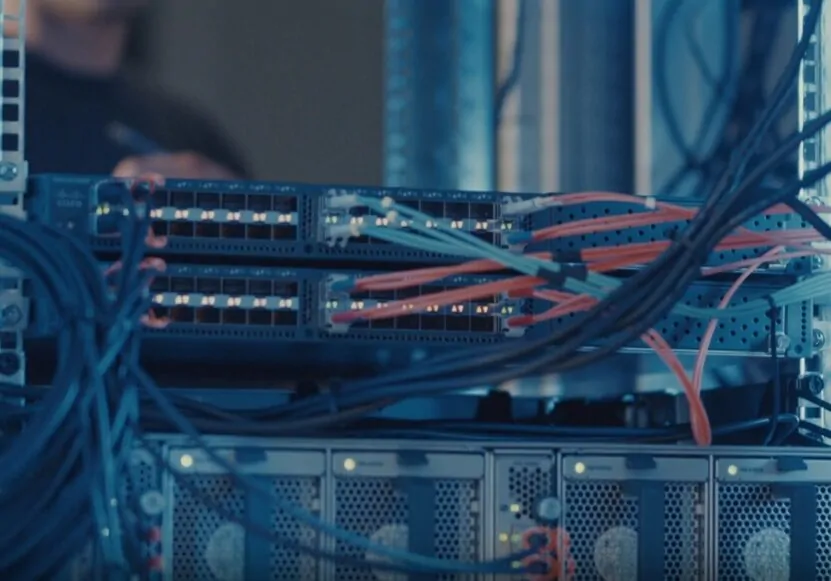
VPNs work by routing your internet connection through a server located elsewhere. This process masks your IP address, making it appear as though you’re accessing the internet from a different location.
This is particularly useful in schools where firewalls block access to certain websites. When you connect to a VPN, the firewall sees the encrypted traffic going to the VPN server, not the actual site you’re visiting.
This encryption also means that your online activities are hidden from network administrators, providing an added layer of privacy.
The technology behind VPNs is quite advanced. They use protocols like OpenVPN, L2TP/IPsec, and PPTP to create a secure tunnel between your device and the internet.
This tunnel encrypts your data, ensuring that it’s protected from anyone who might try to intercept it. The level of encryption varies depending on the VPN provider and protocol, but most offer strong security measures.
What to Do?
- Choose a reputable VPN provider.
- Download and install the VPN software on your device.
- Open the VPN application and sign in using your credentials.
- Select a server location from the list provided by the VPN service.
- Connect to the VPN server to encrypt your internet traffic and hide your IP address.
- Access the internet freely with your school firewall bypassed.
How to Choose the Right VPN?
Selecting the right VPN is crucial. Here are some factors to consider:
- Security: Look for a VPN with strong encryption standards and a no-logs policy.
- Speed: A good VPN should not significantly slow down your internet connection.
- Server Locations: More server locations mean more options for bypassing geographical restrictions.
- Ease of Use: The VPN should be user-friendly, with simple setup and configuration.
- Cost: While there are free VPNs, they might not provide the best security. Paid VPNs often offer better features and protection.
2. Proxy Servers
Proxy servers are one of the oldest and most straightforward methods to bypass school firewalls. They act as intermediaries between your computer and the internet, allowing you to access blocked websites.
How Proxy Servers Function?
A proxy server functions by receiving your internet requests and forwarding them to the desired website. It then returns the site’s response back to you. This process effectively masks your IP address, making it appear as though the request originated from the proxy server, not your device. This is how it manages to bypass firewall restrictions – the school’s network only sees the proxy server’s IP address.
The technology behind proxy servers is less complex than VPNs. They don’t typically encrypt your data, which means they can be faster but less secure. There are different types of proxy servers, like HTTP proxies, which are suitable for web browsing, and SOCKS proxies, which can handle all types of internet traffic but are generally slower.
What to Do?
- Find a reliable proxy server online.
- Note the IP address and port number of the proxy server.
- On your device, open the internet settings.
- Enter the proxy server’s IP address and port number in the proxy settings.
- Save the settings and browse the internet through the proxy server.
How to Choose the Right Proxy Server?
When selecting a proxy server, consider the following:
- Anonymity: Some proxy servers offer more anonymity than others. High-anonymity proxies completely hide your IP address.
- Speed: Since proxies don’t encrypt data, they can be faster than VPNs. However, the speed can vary widely between different proxy services.
- Reliability: Free proxy servers can be less reliable and more likely to be blocked by firewall systems.
- Ease of Use: Look for a proxy server that is easy to set up and use, especially if you’re not familiar with network configurations.
3. DNS Tunneling
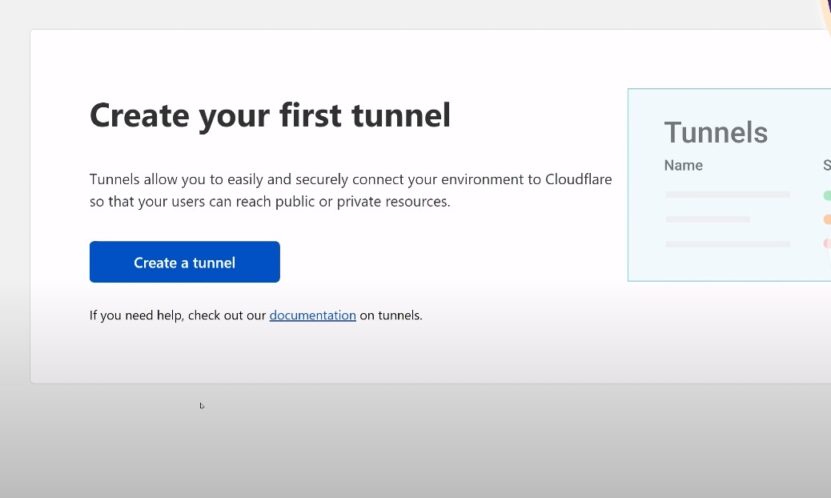
DNS tunneling is a more advanced, yet highly effective method to bypass school firewalls. This technique involves using the Domain Name System (DNS), which is typically unrestricted in most networks, to sneak through the firewall.
How DNS Tunneling Works?
DNS tunneling exploits the way the internet translates domain names into IP addresses. When you enter a website’s name, your device queries a DNS server to get the corresponding IP address. DNS tunneling sends not only the domain name request but also encodes other data (like the website you want to access) within these DNS queries.
Because DNS requests are usually allowed through firewalls for the internet to function correctly, the encoded data in these requests can pass through unnoticed. On the other end, a DNS server designed to recognize and decode these requests retrieves the actual content you want to access and sends it back to your device, disguised as a DNS response.
What to Do?
- Obtain software that facilitates DNS tunneling, such as a DNS tunneling VPN.
- Install the software on your device.
- Configure the DNS settings in the software to connect to a DNS server that supports tunneling.
- Start the DNS tunneling service.
- Use the internet with your DNS queries encoding other data to bypass the firewall.
Considerations for DNS Tunneling
There are several things to consider before using DNS tunneling:
- Complexity: Setting up DNS tunneling can be more complex than using VPNs or proxy servers. It often requires specific technical knowledge.
- Speed: Due to the method of encoding and decoding data, DNS tunneling can be slower compared to other bypass methods.
- Detection and Security: While DNS tunneling can be effective, it’s not entirely undetectable. Also, the lack of encryption in standard DNS queries means that the data you transmit could be intercepted.
4. Tor Network
The Tor network offers a unique approach to bypassing school firewalls, emphasizing anonymity and privacy. Originally developed to protect government communications, Tor is now widely used for a variety of purposes, including accessing the internet without restrictions.
Main Functions
The Tor network, short for “The Onion Router,” operates by routing your internet traffic through a series of volunteer-operated servers around the world. This process, known as onion routing, wraps your data in layers of encryption, similar to the layers of an onion. Each server in the Tor network peels away one layer of encryption, revealing the next server’s address but not the final destination or origin of the data.
This multi-layered approach makes it extremely difficult for anyone to trace your internet activity back to you. When you use Tor to access the internet, your requests appear to come from random nodes in the Tor network, rather than your own IP address. This makes it a powerful tool for bypassing school firewalls, as the network sees only the traffic between you and the Tor entry node, not the sites you ultimately visit.
What to Do?
- Download the Tor Browser from the official website.
- Install the browser on your device.
- Open Tor Browser, and it will connect automatically to the Tor network.
- Once connected, you can browse the internet anonymously and bypass firewall restrictions.
Considerations for Using the Tor Network
When considering the Tor network, keep in mind:
- Anonymity vs. Speed: Tor’s heavy emphasis on anonymity comes with a trade-off in speed. The multiple hops your data takes can significantly slow down your browsing experience.
- Complexity: While using Tor is straightforward once set up, the initial configuration can be more complex than standard proxy or VPN setups.
- Legality and Ethics: Be aware of the legal and ethical implications of using Tor, especially in a school setting. It’s crucial to use this tool responsibly.
5. Mobile Hotspots
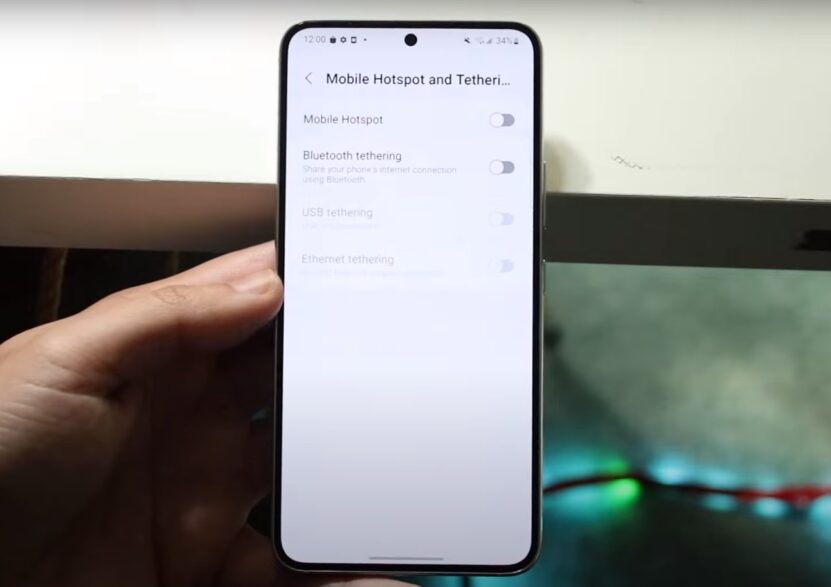
Using a mobile hotspot is a straightforward method to bypass school firewalls. This approach involves leveraging your mobile device’s data connection to access the internet, bypassing the school’s network entirely.
How Mobile Hotspots Work?
A mobile hotspot turns your smartphone or a dedicated hotspot device into a mini Wi-Fi router, allowing other devices like laptops or tablets to connect to the internet using your mobile data plan. When you use a mobile hotspot, you’re not using the school’s network at all; instead, you’re accessing the internet directly through your mobile service provider.
This method is simple and effective because it completely circumvents the school’s firewall. There are no complex configurations or technical skills required – just a device with data connectivity and the ability to share its connection.
What to Do?
- Activate the mobile hotspot feature on your smartphone.
- Set a strong password for the hotspot connection.
- On your device, open the Wi-Fi settings and connect to the mobile hotspot.
- Once connected, use your mobile data to access the internet without restrictions.
Considerations for Using Mobile Hotspots
Before relying on a mobile hotspot, consider the following:
- Data Usage: Be aware of your mobile plan’s data limits. Streaming videos or downloading large files can quickly consume your data allowance.
- Connection Speed: The speed of your mobile hotspot depends on your cellular network’s coverage and strength. In some areas, this might be slower than the school’s Wi-Fi.
- Battery Life: Using your device as a hotspot can drain its battery quickly. Keep a charger or power bank handy.
- Security: Ensure your hotspot has a strong password to prevent unauthorized access.
6. SSH Tunneling
SSH (Secure Shell) tunneling is a method favored by tech-savvy individuals for bypassing school firewalls. It provides a secure and discreet way to access the internet.
How SSH Tunneling Works?
SSH is a network protocol primarily used for secure file transfers and remote server logins. However, it can also be used to tunnel web traffic over an encrypted connection. In SSH tunneling, an SSH client creates an encrypted tunnel between your computer and an SSH server. Your web requests are sent through this tunnel, emerging from the server on the other side.
This method effectively bypasses the school firewall, as the only visible traffic is the encrypted connection to the SSH server. The actual sites you visit remain hidden. Furthermore, because SSH is commonly used for legitimate purposes, traffic to and from SSH servers is less likely to be blocked by school firewalls.
What to Do?
- Obtain access to an SSH server.
- Download and install an SSH client on your device.
- Configure the SSH client with the server’s IP address, your username, and password.
- Establish an SSH connection to create a secure tunnel.
- Configure your browser or device to use the SSH tunnel for internet traffic.
When to Use It?
Here are some important points to consider when using SSH tunneling:
- Technical Skill Required: Setting up an SSH tunnel requires more technical knowledge compared to using VPNs or proxy servers.
- Finding an SSH Server: You’ll need access to an SSH server. This can be your own server or one provided by a third party.
- Speed and Reliability: SSH tunnels can be quite fast and reliable, but this depends on the SSH server’s quality and location.
- Security: While SSH tunneling is secure, remember that the end-to-end encryption only extends to the SSH server. Beyond that, your traffic is unencrypted unless the website uses HTTPS.
7. Browser Extensions

Browser extensions offer an easy and accessible way to bypass school firewalls. These lightweight tools can be added directly to your web browser, providing a hassle-free solution for accessing restricted content.
How Browser Extensions Work?
Browser extensions that help bypass firewalls typically function as proxies or VPNs. Once installed, they allow you to route your browser traffic through servers located elsewhere, thus bypassing the restrictions imposed by the school’s network. These extensions can be activated or deactivated with a simple click, making them very user-friendly.
The ease of installation is one of the biggest advantages of browser extensions. Most popular web browsers like Chrome, Firefox, and Edge support a range of extensions that can be easily added from their respective web stores. Moreover, these extensions often offer a selection of server locations, giving you the flexibility to choose the most effective one for bypassing specific restrictions.
What to Do?
- Choose a browser that supports extensions, such as Chrome or Firefox.
- Visit the browser’s web store and search for a VPN or proxy extension.
- Add the extension to your browser.
- Activate the extension and select a server or proxy to connect through.
- Browse the internet with the firewall bypassed.
Considerations for Using Browser Extensions
When using browser extensions for firewall bypass, consider the following:
- Security and Privacy: Not all extensions offer the same level of security. Look for extensions with a good reputation and positive reviews.
- Speed Impact: Some extensions may slow down your browsing speed, depending on the proxy or VPN server’s quality.
- Ease of Use: Opt for extensions that are straightforward to configure and use.
- Compatibility: Ensure the extension is compatible with your browser and the websites you wish to access.
8. Changing Network Settings
Altering network settings is a more technical, yet effective method for bypassing school firewalls. This approach involves modifying certain configurations on your device to reroute your internet traffic.
How to Change Them?
This method usually involves altering your device’s DNS settings. By default, your device uses the DNS provided by the school’s network, which is where the restrictions are enforced. Changing the DNS to a different, unrestricted service like Google DNS or OpenDNS can provide access to blocked sites.
Another way to change network settings is by adjusting your device’s proxy settings. This method involves routing your internet traffic through a different proxy server, similar to how browser extensions work, but on a system-wide level. Both DNS and proxy changes can be effective in bypassing firewalls, but they require some technical understanding of network configurations.
What to Do?
- Open the network settings on your device.
- Locate the DNS settings and change them to a public DNS like Google DNS (8.8.8.8 and 8.8.4.4) or OpenDNS.
- Save the settings and restart your network connection.
- Access the internet with the new DNS, bypassing content restrictions.
When To Use It?
When considering changing network settings, keep in mind:
- Technical Knowledge: You need to understand network settings and how to modify them safely.
- Device Access: Administrative access to your device is necessary to change these settings.
- Network Impact: Be aware of how these changes might affect other network-related functions on your device.
- Reversibility: Ensure you know how to revert the settings back to their original state if needed.
9. Cloud-Based Services

Cloud-based services have emerged as an innovative way to bypass school firewalls, especially for collaborative and educational purposes. Services like Google Drive, Dropbox, and various online collaboration platforms can often be accessed even through restrictive school networks.
How These Services Work?
Cloud services often remain accessible in school environments because they are widely used for legitimate educational and work-related purposes. By utilizing these services, you can access, store, and share information that might be otherwise blocked on a school’s network. For instance, educational materials, videos, or websites can be shared via Google Drive links or accessed through collaborative platforms like Microsoft Teams or Slack.
The key here is that these services use standard web protocols and are hosted on domains that are typically not blocked by school firewalls. This makes them ideal for indirectly accessing restricted content or collaborating on projects that require internet resources which might be blocked on the school’s network.
What to Do?
- Choose a cloud service like Google Drive or Microsoft Teams.
- Upload the files or links you need to access to the cloud service.
Access these files or links from any device, bypassing the school’s firewall restrictions on direct site access.
Considerations for Using Cloud-Based Services
When using cloud-based services, consider the following:
- Content Accessibility: While these services can bypass certain restrictions, they may not be suitable for accessing all types of blocked content.
- Data Security: Be mindful of the privacy and security of the information you store and share on these platforms.
- Ethical Use: Always use cloud services responsibly and in accordance with your school’s policies and guidelines.
- Dependency on Internet Connectivity: These services require a stable internet connection and can be impacted by network speeds.
10. Using Decentralized Networks
Decentralized networks offer a sophisticated method for bypassing school firewalls, providing an innovative solution for students needing unrestricted access to educational resources. Utilizing technologies like blockchain-based decentralized applications (DApps) and peer-to-peer systems, these networks operate without centralized control, making them less susceptible to traditional network restrictions.
To further enhance the effectiveness of decentralized networks in a school setting, integrating a service like NinjasProxy can be extremely beneficial. NinjasProxy offers private proxies that can be used to navigate through decentralized networks more securely and efficiently.
By routing your requests through NinjasProxy’s private proxies, you can ensure that your connection to decentralized nodes remains stable and undetected by school firewalls.
What to Do?
- Find a decentralized network or application that fits your needs, such as a blockchain-based DApp.
- Download and install the necessary software or client.
- Connect to the network by following the specific instructions provided for the decentralized service.
- Use the decentralized network to access or share information freely without firewall restrictions.
FAQs
Last Words
It’s crucial to remember that while bypassing firewalls can sometimes be necessary to access legitimate educational content, it should always be done responsibly and within the boundaries of legal and ethical guidelines.
Schools implement firewalls primarily to ensure a safe and focused learning environment, and any attempt to circumvent these measures should be weighed against the potential risks and consequences.
Related Posts:
- 10 Best Online Tutoring Methods Teachers Can Use in 2025
- Top 10 Free Online IQ Tests You Can Take Right Now
- The Truth About Online University Programs - Can You…
- What Are the Limits of Learning Online? Can You…
- How Many Times Can You Take the SAT - Is There a Limit?
- How to Safely Bypass Your Screen Time Passcode